Is SMTP port 25 secure?
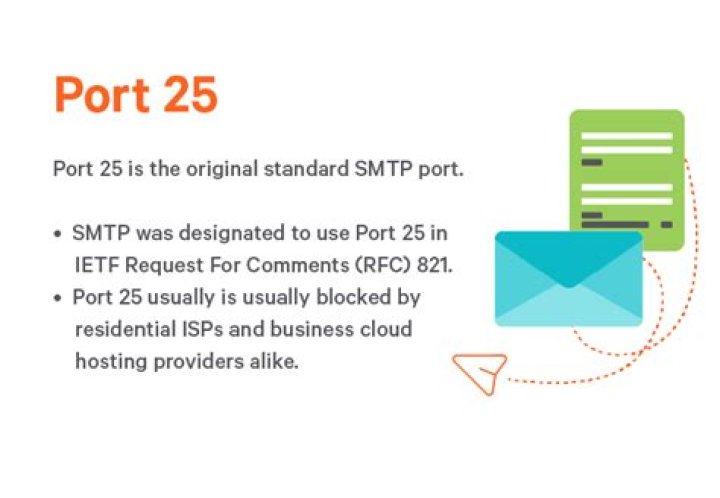
SMTP was designated to use port 25 in IETF Request For Comments (RFC) 821. IANA still recognizes Port 25 as the standard, default SMTP port. The port is no longer recognized by IANA. This port has secure according to the guidelines set out by the IETF.
Should I use port 25 SMTP?
Which port should you use for SMTP? Ports 25, 465, 587, or 2525 for SMTP have all been considered standard SMTP ports at some point, but only 587 or 2525 really should be considered for modern use.Is SMTP secured?
SMTP can be secured through the enablement of TLS on your mail server. By enabling TLS, you are encrypting the SMTP protocol on the transport layer by wrapping SMTP inside of a TLS connection. This effectively secures SMTP and transforms it into SMTPS. Port 587 and 465 are both frequently used for SMTPS traffic.What is the SMTP server to port 25?
Port 25: SMTP port 25 continues to be used primarily for SMTP relaying. SMTP relaying is the transmission of email from email server to email server. In most cases, modern SMTP email clients (Microsoft Outlook, Mail, Thunderbird, etc.)What is the secure port number for SMTP?
Common SMTP ports:SMTP - port 25 or 2525 or 587. Secure SMTP (SSL / TLS) - port 465 or 25 or 587, 2526 (Elastic Email)
SMTP Ports Explained in Minutes (Example: Gmail SMTP)
What is difference between SMTP port 25 and 587?
SMTP Port 587Whereas port 25 is the recommended port number for SMTP communications between mail servers (i.e., for relaying messages), port 587 is the one recommended for message submissions by mail clients to mail servers.
Can I use port 587 instead 25?
Port 25 is commonly used for SMTP relay, but you should not use it for SMTP submission because most providers block it. If you want to configure your WordPress site or email client to use SMTP, you should start with port 587 as your first choice, as it's the standard port for SMTP submission.Should I open SMTP port?
Port 25 needs to be open in order for it to receive mail from the internet. All mail servers will establish a connection on port 25 and initiate TLS (encryption) on that port if necessary. Secure SMTP (port 465) is used only by clients connecting to your server in order to send mail out.How do I choose my SMTP port?
Windows Mail
- Start Windows Mail, click the Tools menu at the top of the window and then click Accounts.
- Select your account under Mail, and then click on the Properties button.
- Go to the Advanced tab, under Outgoing server (SMTP), change port 25 to 587.
- Click the OK button to save the changes.
How do I open port 25?
Click the "Start" button and choose "Control Panel." Click "Windows Firewall" and then click the tab titled "Exceptions." Choose "Add Port." In the text box marked "Name," enter the name of your email server. Type the number "25" in the text box named "Port."What are the vulnerabilities of SMTP?
What are the threats to SMTP security?
- Unauthorized access to your emails and data leakage. Cybercriminals might try to get access to your SMTP server that all the outgoing mail goes through. ...
- Spam and Phishing. ...
- Malware. ...
- DoS attacks. ...
- S/MIME. ...
- PGP. ...
- Bitmessage.
What is the most common cause of SMTP server vulnerability?
What is the most common cause of SMTP server vulnerability? The server is not configured correctly.How do I know if SMTP is SSL?
You can see if a SMTP server has STARTTLS enabled by connecting to it on port 25 and issuing the EHLO command as Dan explains elsewhere on this page. Both SSL and TLS are just encryption protocols, TLS being the successor to SSL.Why is port 25 blocked by ISP?
The standard port used for SMTP connections is 25. An ISP (Internet Service Provider) may block port 25 in order to prevent spamming by its customers. With port 25 being blocked, you won't be able to host your own mail server at home or work.Is port 25 plain text?
Initially, a server-to-server SMTP connection is always in plain text on port 25.How can an SMTP server be exploited?
SMTP VulnerabilitiesAttackers can gain unauthorized access to your SMTP server in several ways, including: Phishing and malware: A user within your organization may have downloaded a malware-infected file or clicked a malicious link, allowing threat actors to harvest their credentials.